AWS IoT VPN: A Comprehensive Guide to Secure and Efficient IoT Connectivity
In today's interconnected world, AWS IoT VPN plays a pivotal role in ensuring secure communication between devices and cloud platforms. As the Internet of Things (IoT) continues to expand, organizations are increasingly seeking robust solutions to manage and secure their IoT ecosystems. AWS IoT offers a suite of tools that address these challenges, and incorporating a virtual private network (VPN) enhances security while maintaining efficiency.
From smart homes to industrial automation, IoT devices generate vast amounts of data that require secure transmission. This is where AWS IoT VPN becomes indispensable. By integrating a VPN with AWS IoT, businesses can create a secure tunnel for data exchange, protecting sensitive information from unauthorized access and cyber threats.
This article will delve into the intricacies of AWS IoT VPN, exploring its benefits, implementation strategies, and best practices. Whether you're a tech enthusiast, a business owner, or an IT professional, understanding AWS IoT VPN can help you harness the full potential of IoT technology while ensuring top-notch security.
Introduction to AWS IoT
AWS IoT is a cloud platform designed to facilitate the connection, management, and secure interaction of IoT devices. It allows developers and businesses to build IoT applications that can scale effortlessly, handling millions of devices and trillions of messages. The platform offers a range of services, including device management, data processing, and analytics, all within a secure environment.
Core Features of AWS IoT
AWS IoT provides several key features that make it a preferred choice for IoT deployments:
- Device Gateway: Enables secure and efficient communication between devices and AWS services.
- Device Shadow: Maintains a synchronized state of devices, allowing control even when they are offline.
- Rules Engine: Processes and routes IoT data to other AWS services for further analysis and action.
These features, combined with the scalability and reliability of AWS, make it an ideal platform for IoT solutions. However, ensuring secure communication is paramount, which is where AWS IoT VPN comes into play.
What is AWS IoT VPN?
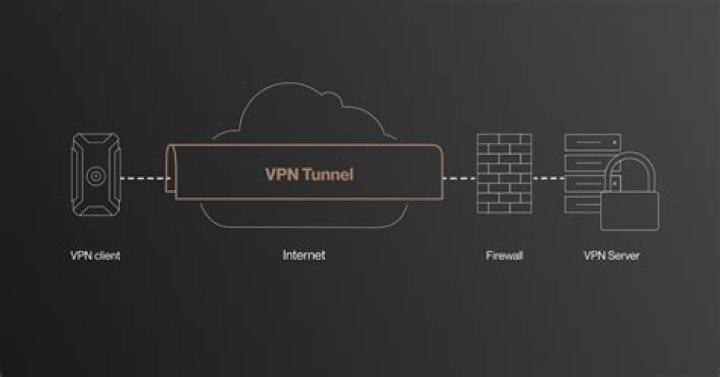
AWS IoT VPN refers to the integration of a virtual private network with AWS IoT services. This setup creates a secure, encrypted tunnel between IoT devices and the AWS cloud, ensuring that all data transmitted is protected from unauthorized access. By leveraging AWS IoT VPN, organizations can enhance the security of their IoT infrastructure without compromising performance.
How Does AWS IoT VPN Work?
When an IoT device connects to AWS IoT through a VPN, the data is encrypted before transmission. The encrypted data is then routed through the secure tunnel to the AWS cloud, where it is decrypted and processed. This process ensures that even if the data is intercepted during transmission, it remains unreadable to unauthorized parties.
Additionally, AWS IoT VPN supports various authentication methods, including certificates and mutual TLS, to verify the identity of devices and prevent unauthorized access. This multi-layered security approach is crucial for protecting sensitive IoT data.
Benefits of AWS IoT VPN
Incorporating AWS IoT VPN into your IoT infrastructure offers numerous advantages:
- Enhanced Security: Protects data from interception and unauthorized access.
- Scalability: Handles large volumes of data and devices effortlessly.
- Reliability: Ensures consistent and stable communication between devices and the cloud.
- Compliance: Helps meet industry standards and regulations for data protection.
These benefits make AWS IoT VPN an attractive solution for businesses looking to secure their IoT ecosystems while maintaining operational efficiency.
How to Implement AWS IoT VPN
Implementing AWS IoT VPN involves several steps, from setting up the infrastructure to configuring devices:
Step 1: Set Up the AWS IoT Environment
Begin by creating an AWS IoT environment in your AWS account. This includes setting up the necessary resources, such as IoT Core, rules engine, and device shadows.
Step 2: Configure the VPN
Next, configure a virtual private network that connects to your AWS IoT environment. This can be done using AWS services like AWS Client VPN or by integrating third-party solutions.
Step 3: Secure Device Authentication
Ensure that all devices connecting to the AWS IoT environment are properly authenticated. Use certificates and mutual TLS for secure device identification.
Step 4: Test and Monitor
Finally, test the setup to ensure that data is transmitted securely and efficiently. Monitor the system regularly to identify and address any potential issues.
AWS IoT VPN Security Features
AWS IoT VPN incorporates several advanced security features to protect IoT data:
- Encryption: Data is encrypted during transmission using industry-standard protocols.
- Authentication: Devices are authenticated using certificates and mutual TLS to prevent unauthorized access.
- Access Control: Fine-grained access control policies ensure that only authorized devices and users can access the network.
These features collectively enhance the security posture of IoT deployments, making them more resilient to cyber threats.
Cost Considerations
While AWS IoT VPN offers significant benefits, it's essential to consider the associated costs:
- Infrastructure Costs: Setting up and maintaining the necessary infrastructure can incur costs.
- Data Transfer Costs: Data transmitted over the VPN may incur additional charges based on usage.
- Management Costs: Ongoing management and monitoring of the system may require additional resources.
However, these costs are often offset by the enhanced security and operational efficiency provided by AWS IoT VPN.
Best Practices for AWS IoT VPN
To maximize the benefits of AWS IoT VPN, consider the following best practices:
- Regularly update and patch devices to address security vulnerabilities.
- Implement strong authentication and access control policies.
- Monitor network activity to detect and respond to potential threats.
- Conduct regular security audits to ensure compliance with industry standards.
By adhering to these practices, organizations can maintain a secure and efficient IoT infrastructure.
Common Issues and Troubleshooting
While AWS IoT VPN is a robust solution, issues may arise during implementation and operation. Common problems include:
- Connection Issues: Devices may fail to connect due to incorrect configurations or network problems.
- Performance Bottlenecks: High data volumes can lead to performance degradation.
- Security Breaches: Unauthorized access attempts may occur despite security measures.
To address these issues, ensure thorough testing and monitoring, and promptly apply updates and patches as needed.
Comparison with Other Solutions
When evaluating IoT security solutions, it's important to compare AWS IoT VPN with other options:
Comparison Table
| Feature | AWS IoT VPN | Other Solutions |
|---|---|---|
| Security | High | Varies |
| Scalability | Excellent | Limited |
| Integration | Seamless | Complex |
AWS IoT VPN stands out due to its superior security, scalability, and ease of integration with other AWS services.
Future of AWS IoT VPN
As IoT technology continues to evolve, AWS IoT VPN will play an increasingly critical role in securing IoT ecosystems. Future advancements may include enhanced encryption protocols, improved device authentication methods, and more efficient data processing capabilities.
Staying informed about these developments will help organizations leverage AWS IoT VPN to its fullest potential, ensuring secure and efficient IoT operations in the years to come.
Conclusion
In summary, AWS IoT VPN is a powerful tool for securing IoT communications. By providing enhanced security, scalability, and reliability, it addresses the challenges faced by organizations deploying IoT solutions. Implementing AWS IoT VPN involves careful planning and adherence to best practices, but the benefits far outweigh the efforts.
We invite you to share your thoughts and experiences with AWS IoT VPN in the comments below. Additionally, explore other articles on our site to deepen your understanding of IoT technologies and their applications.


