Best RemoteIoTSH Key Management: A Comprehensive Guide to Secure Your IoT Network
RemoteIoTSH key management has become a critical focus for businesses and organizations as IoT devices continue to proliferate across industries. In today's digital landscape, securing sensitive data and ensuring the integrity of IoT networks is paramount. Poor key management practices can expose networks to cyber threats, compromising sensitive information and disrupting operations.
With the rapid growth of IoT ecosystems, the need for robust key management solutions has never been more pressing. Businesses must adopt best practices to safeguard their networks and devices. This guide will provide an in-depth exploration of the best RemoteIoTSH key management strategies, highlighting critical aspects to consider when securing your IoT infrastructure.
In this article, we will delve into the importance of secure key management, explore the latest tools and technologies, and offer actionable advice to help you implement a secure and efficient RemoteIoTSH key management system. Whether you're a network administrator or a decision-maker, this guide will equip you with the knowledge to protect your IoT ecosystem effectively.
Overview of RemoteIoTSH Key Management
RemoteIoTSH key management refers to the processes and technologies used to securely store, distribute, and manage cryptographic keys in IoT environments. These keys are essential for encrypting data, ensuring secure communications, and authenticating devices within an IoT network. Proper key management practices are crucial to maintaining the confidentiality, integrity, and availability of sensitive information.
As IoT devices become more interconnected, the complexity of managing cryptographic keys increases. A well-designed key management system must address scalability, security, and ease of use. By implementing a robust RemoteIoTSH key management solution, organizations can reduce the risk of data breaches and ensure compliance with industry standards.
Key Management in IoT Networks
In IoT networks, key management plays a vital role in securing communications between devices, gateways, and cloud platforms. Cryptographic keys are used for various purposes, including:
- Data encryption
- Device authentication
- Secure firmware updates
- Access control
Effective key management ensures that only authorized devices and users can access sensitive information, reducing the risk of unauthorized access and cyberattacks.
Why Is Key Management Important for IoT Networks?
In the realm of IoT, key management is not just a technical requirement but a fundamental aspect of network security. Poor key management practices can lead to severe consequences, including data breaches, financial losses, and reputational damage. Organizations must prioritize key management to protect their IoT ecosystems from cyber threats.
Here are some reasons why key management is critical for IoT networks:
- Confidentiality: Cryptographic keys ensure that sensitive data remains private and secure.
- Integrity: Keys help verify the authenticity of data, preventing tampering and unauthorized modifications.
- Availability: Proper key management ensures that devices and systems remain operational, even in the face of cyberattacks.
Challenges in RemoteIoTSH Key Management
Managing cryptographic keys in IoT environments presents several challenges. These challenges stem from the unique characteristics of IoT networks, such as the large number of devices, diverse communication protocols, and limited computational resources. Some of the key challenges include:
- Scalability: IoT networks often consist of thousands or even millions of devices, making it difficult to manage keys efficiently.
- Device Heterogeneity: IoT devices come in various forms and capabilities, complicating the implementation of a unified key management system.
- Resource Constraints: Many IoT devices have limited processing power and memory, which can hinder the execution of complex cryptographic algorithms.
Overcoming Key Management Challenges
To address these challenges, organizations must adopt innovative solutions that balance security, scalability, and performance. Some strategies include:
- Implementing hardware-based security modules
- Using lightweight cryptographic algorithms
- Adopting cloud-based key management solutions
Best Solutions for RemoteIoTSH Key Management
Several solutions are available to help organizations implement effective RemoteIoTSH key management. These solutions range from hardware-based security modules to cloud-based platforms, each offering unique advantages and disadvantages. Below are some of the best solutions for managing cryptographic keys in IoT networks:
HSM (Hardware Security Module)
HSMs are specialized hardware devices designed to securely store and manage cryptographic keys. They provide a high level of security and are ideal for organizations with stringent security requirements. However, HSMs can be expensive and may require significant upfront investment.
Cloud-Based Key Management
Cloud-based key management solutions offer scalability and flexibility, making them suitable for large IoT networks. These solutions allow organizations to manage keys from a centralized platform, reducing the administrative burden. However, reliance on third-party cloud providers may raise concerns about data privacy and security.
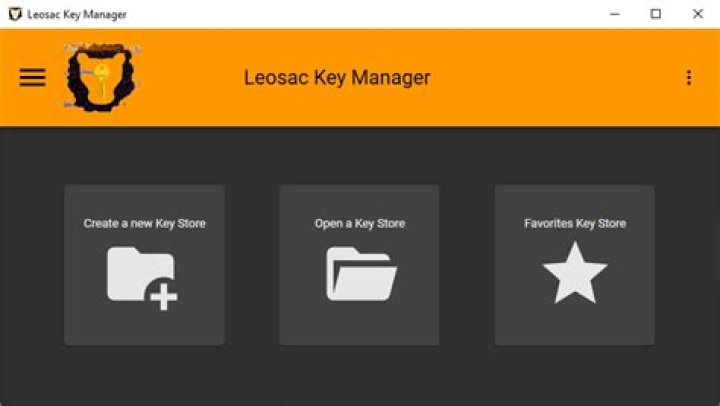
Top Tools for Secure Key Management
Several tools and platforms are available to assist organizations in managing cryptographic keys in IoT networks. These tools offer a range of features, including key generation, storage, distribution, and revocation. Some of the top tools for secure key management include:
- AWS Key Management Service (KMS)
- Google Cloud Key Management Service
- Thales Luna HSM
- Microsoft Azure Key Vault
Features to Look for in Key Management Tools
When selecting a key management tool, consider the following features:
- Scalability: Ensure the tool can handle the size and complexity of your IoT network.
- Compliance: Verify that the tool complies with relevant industry standards and regulations.
- Usability: Choose a tool with an intuitive interface and easy-to-use features.
Best Practices for Key Management in IoT
Implementing best practices for key management is essential to ensuring the security of your IoT network. Here are some key practices to follow:
- Use strong, randomly generated keys
- Regularly rotate keys to minimize the risk of compromise
- Implement access controls to restrict key usage
- Monitor key usage and revoke keys when necessary
Key Lifecycle Management
Effective key management involves managing the entire lifecycle of cryptographic keys, from creation to destruction. This includes:
- Key generation
- Key distribution
- Key storage
- Key revocation
Data Privacy and Compliance in Key Management
Data privacy and compliance are critical considerations in RemoteIoTSH key management. Organizations must ensure that their key management practices adhere to relevant regulations, such as GDPR, HIPAA, and CCPA. Failure to comply with these regulations can result in hefty fines and legal consequences.
Ensuring Compliance with Industry Standards
To ensure compliance, organizations should:
- Regularly audit their key management processes
- Implement encryption standards such as AES and RSA
- Adopt industry-recognized security frameworks
Security Tips for RemoteIoTSH Networks
In addition to effective key management, organizations should adopt other security measures to protect their IoT networks. Some security tips include:
- Use strong authentication mechanisms
- Regularly update firmware and software
- Implement network segmentation
- Conduct regular security assessments
Securing IoT Devices
Securing IoT devices is a critical component of network security. Organizations should:
- Use tamper-resistant hardware
- Implement secure boot processes
- Monitor device behavior for anomalies
Future Trends in IoT Key Management
The field of IoT key management is rapidly evolving, with new technologies and innovations emerging to address existing challenges. Some future trends in IoT key management include:
- Quantum-resistant cryptography
- Blockchain-based key management
- AI-driven security solutions
Preparing for the Future
To prepare for the future of IoT key management, organizations should:
- Stay informed about the latest developments in cryptography
- Invest in emerging technologies and solutions
- Collaborate with industry experts and researchers
Conclusion and Call to Action
In conclusion, RemoteIoTSH key management is a critical aspect of securing IoT networks. By implementing best practices, adopting the right tools, and staying informed about emerging trends, organizations can protect their IoT ecosystems from cyber threats. Remember that key management is not a one-time task but an ongoing process that requires vigilance and commitment.
We encourage you to take action by reviewing your current key management practices and identifying areas for improvement. Share your thoughts and experiences in the comments below, and don't forget to explore other articles on our site for more insights into IoT security and beyond.



