How to Effectively Manage IoT Behind a Firewall: A Comprehensive Guide
Managing IoT devices behind a firewall is crucial for ensuring robust cybersecurity and protecting sensitive data in modern network environments. As the Internet of Things (IoT) continues to grow exponentially, businesses and individuals face increasing challenges in securing their connected devices. A firewall acts as the first line of defense, controlling inbound and outbound network traffic and protecting networks from unauthorized access.
In this digital age, the integration of IoT devices into everyday operations has transformed industries and improved efficiency. However, these devices also introduce vulnerabilities that malicious actors can exploit. That’s why understanding how to manage IoT devices behind a firewall is essential for safeguarding your network infrastructure.
This article will provide a detailed exploration of managing IoT devices within a firewall-protected environment. You’ll learn about the importance of firewalls, best practices for securing IoT devices, and actionable strategies to protect your network. Whether you're a small business owner or an IT professional, this guide will equip you with the knowledge needed to enhance your cybersecurity posture.
The Importance of Managing IoT Devices Behind a Firewall
The proliferation of IoT devices has created a new era of connectivity, but it has also introduced significant security challenges. Firewalls play a critical role in protecting these devices from external threats. By managing IoT devices behind a firewall, organizations can:
- Prevent unauthorized access to sensitive data.
- Control network traffic and monitor device activity.
- Protect against malware and other cyber threats.
- Ensure compliance with industry regulations.
Without proper firewall management, IoT devices can become easy targets for hackers. For example, a compromised IoT device could serve as a gateway for attackers to infiltrate an entire network. This underscores the importance of implementing robust firewall strategies to safeguard IoT devices.
Understanding Firewalls and Their Role in IoT Security
A firewall is a security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. When managing IoT devices, firewalls act as a barrier between the internal network and external threats. They help:
- Filter traffic to block malicious activity.
- Inspect packets for potential threats.
- Enforce security policies for IoT devices.
Firewalls are particularly important for IoT devices because these devices often lack advanced security features. By integrating firewalls into the network infrastructure, organizations can better manage and secure their IoT deployments.
Types of Firewalls
There are several types of firewalls, each with its own strengths and weaknesses:
- Packet-filtering firewalls: Inspect individual packets for specific criteria.
- Stateful inspection firewalls: Track active connections to ensure data integrity.
- Next-generation firewalls (NGFW): Combine traditional firewall capabilities with advanced features like deep packet inspection.
Common IoT Threats Behind a Firewall
Even with a firewall in place, IoT devices can still be vulnerable to various threats. Some common IoT threats include:
- DDoS attacks: Hackers can use compromised IoT devices to launch distributed denial-of-service attacks.
- Malware infections: Vulnerable devices can be infected with malware, leading to data breaches.
- Firmware vulnerabilities: Outdated firmware can expose devices to exploitation.
To mitigate these threats, organizations must adopt proactive security measures, including regular updates and thorough monitoring.
Best Practices for Managing IoT Behind a Firewall
Implementing best practices is essential for effectively managing IoT devices behind a firewall. Here are some key strategies:
1. Implement Strong Authentication
Ensure that all IoT devices require strong authentication before accessing the network. This can include:
- Multi-factor authentication (MFA).
- Unique credentials for each device.
- Regular password updates.
2. Regularly Update Firmware
Keeping IoT device firmware up-to-date is crucial for addressing known vulnerabilities. Regular updates help ensure that devices are protected against the latest threats.
3. Use Encryption
Encrypting data transmitted between IoT devices and the network can prevent unauthorized access. This is especially important for sensitive information.
Tools for Managing IoT Devices Behind a Firewall
Several tools are available to help manage IoT devices within a firewall-protected environment. These tools can assist with:
- Network monitoring.
- Device management.
- Security policy enforcement.
Some popular tools include:
- Snort: An open-source intrusion detection system.
- Palo Alto Networks: A comprehensive firewall solution for IoT security.
- Cisco ASA: A firewall appliance designed for advanced threat protection.
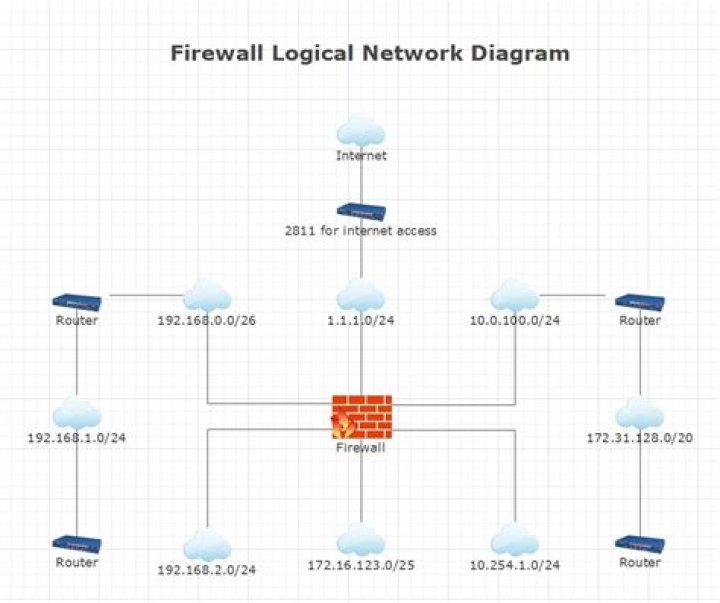
Network Segmentation for IoT Devices
Network segmentation involves dividing a network into smaller subnetworks to enhance security and improve performance. By segmenting IoT devices, organizations can:
- Limit the impact of a security breach.
- Control access to sensitive data.
- Optimize network traffic flow.
Implementing network segmentation is a critical step in managing IoT devices behind a firewall.
Benefits of Network Segmentation
Some key benefits of network segmentation include:
- Improved security posture.
- Enhanced network performance.
- Greater control over device access.
Developing a Firewall Policy for IoT Devices
A well-defined firewall policy is essential for managing IoT devices effectively. This policy should include:
- Clear rules for inbound and outbound traffic.
- Specific guidelines for device access.
- Regular audits and updates.
By establishing a comprehensive firewall policy, organizations can ensure consistent security across their IoT deployments.
Monitoring and Analyzing IoT Traffic Behind a Firewall
Continuous monitoring is crucial for detecting and responding to potential threats. Organizations should implement tools and processes for:
- Real-time traffic analysis.
- Alerting on suspicious activity.
- Generating detailed reports.
Effective monitoring helps organizations stay ahead of emerging threats and maintain a secure network environment.
Best Tools for Monitoring IoT Traffic
Some of the best tools for monitoring IoT traffic include:
- Splunk: A powerful analytics platform for network data.
- Wireshark: A network protocol analyzer for deep packet inspection.
- ELK Stack: A suite of open-source tools for log analysis.
Regularly Updating Firewalls and IoT Devices
Keeping firewalls and IoT devices up-to-date is essential for maintaining security. Regular updates should include:
- Firmware patches for IoT devices.
- Security rule updates for firewalls.
- Software upgrades for monitoring tools.
By staying current with updates, organizations can protect against the latest threats and vulnerabilities.
The Future of IoT and Firewall Management
As IoT continues to evolve, so too will the methods for managing devices behind firewalls. Emerging technologies like artificial intelligence (AI) and machine learning (ML) are expected to play a significant role in enhancing IoT security. These technologies can:
- Predict and prevent potential threats.
- Automate security processes.
- Improve threat detection accuracy.
Looking ahead, organizations must remain vigilant and adaptable to stay ahead of the ever-changing cybersecurity landscape.
Conclusion
Managing IoT devices behind a firewall is a critical component of modern cybersecurity strategies. By implementing best practices, leveraging advanced tools, and staying informed about emerging trends, organizations can effectively protect their networks and data. Remember to:
- Implement strong authentication and encryption.
- Regularly update firewalls and IoT devices.
- Monitor network traffic for suspicious activity.
We encourage you to share your thoughts and experiences in the comments below. Additionally, feel free to explore other articles on our site for more insights into cybersecurity and IoT management. Together, we can build a safer digital future!
Data Sources:


