How to Effectively Manage IoT Behind Firewall for Enhanced Security
As the Internet of Things (IoT) continues to expand, managing IoT devices behind a firewall has become a critical necessity for businesses and individuals alike. IoT devices are revolutionizing the way we live and work, but they also introduce new security challenges. Without proper management, these devices can become entry points for cyberattacks, compromising sensitive data and network integrity. In this article, we will explore the best strategies to manage IoT devices behind a firewall, ensuring robust security and seamless functionality.
The increasing adoption of IoT devices in homes, offices, and industries has created a complex digital landscape. While these devices offer convenience and efficiency, they also pose significant risks if not properly secured. Managing IoT devices behind a firewall is a proactive approach to mitigate these risks and safeguard your network infrastructure.
This article aims to provide comprehensive insights into the world of IoT security, focusing on firewall management. By the end of this article, you will have a clear understanding of how to secure your IoT devices, enhance network performance, and protect sensitive data. Whether you're a business owner, IT professional, or a tech-savvy individual, this guide will equip you with the knowledge and tools to manage IoT devices effectively.
Understanding IoT and Its Security Challenges
What is IoT?
The Internet of Things (IoT) refers to the network of interconnected physical devices that can communicate and exchange data over the internet. These devices range from smart home appliances to industrial sensors, all designed to enhance automation and efficiency. However, the rapid growth of IoT has brought about significant security challenges.
IoT devices often lack robust security features, making them vulnerable to cyber threats. Hackers can exploit these vulnerabilities to gain unauthorized access to networks, steal sensitive information, or launch large-scale attacks. Managing IoT devices behind a firewall is essential to address these security concerns.
Common IoT Security Challenges
Here are some of the most common security challenges associated with IoT devices:
- Weak Authentication: Many IoT devices come with default passwords that are rarely changed, making them easy targets for attackers.
- Limited Encryption: Some IoT devices lack proper encryption protocols, leaving data transmissions exposed to interception.
- Firmware Vulnerabilities: Outdated firmware can contain security flaws that attackers can exploit.
- Network Exposure: IoT devices that are not properly isolated can expose the entire network to potential threats.
Why Managing IoT Behind a Firewall is Essential
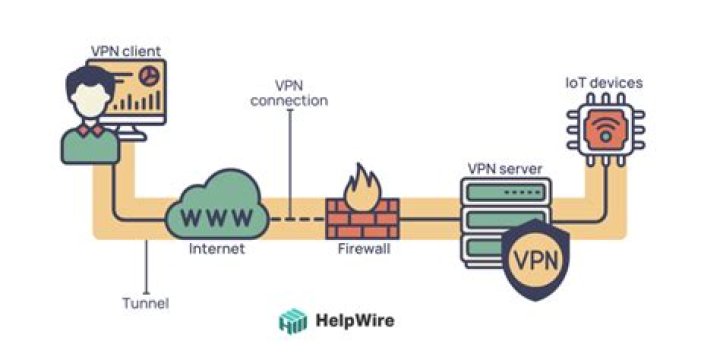
Managing IoT devices behind a firewall is crucial for maintaining network security. A firewall acts as a barrier between your internal network and external threats, monitoring and controlling incoming and outgoing network traffic based on predetermined security rules.
By placing IoT devices behind a firewall, you can:
- Restrict unauthorized access to your network.
- Monitor device activity and detect suspicious behavior.
- Segment IoT devices into separate networks to minimize risks.
- Ensure compliance with industry standards and regulations.
Setting Up a Firewall for IoT Devices
Choosing the Right Firewall
Selecting the appropriate firewall is the first step in securing your IoT devices. Modern firewalls offer advanced features such as intrusion detection, deep packet inspection, and application control. When choosing a firewall, consider the following factors:
- Scalability to accommodate growing IoT deployments.
- Support for IoT-specific protocols and standards.
- Compatibility with existing network infrastructure.
- Ease of management and configuration.
Configuring the Firewall
Proper configuration is essential to maximize the effectiveness of your firewall. Follow these steps to configure your firewall for IoT devices:
- Identify all IoT devices on your network and their communication requirements.
- Set up rules to allow only necessary traffic to and from IoT devices.
- Segment IoT devices into a dedicated subnet to isolate them from other network devices.
- Regularly update firewall rules to adapt to changing security needs.
Best Practices for Managing IoT Behind a Firewall
Implementing Network Segmentation
Network segmentation is a critical strategy for managing IoT devices behind a firewall. By isolating IoT devices into a separate network segment, you can:
- Limit the potential impact of a compromised IoT device.
- Apply specific security policies to IoT devices without affecting other network devices.
- Monitor IoT traffic independently for better visibility and control.
Regularly Updating Firmware
Keeping IoT device firmware up to date is essential for addressing security vulnerabilities. Manufacturers frequently release firmware updates that include security patches and improvements. Establish a routine for checking and applying firmware updates to all IoT devices on your network.
Using Strong Authentication
Implementing strong authentication mechanisms is vital for securing IoT devices. Consider using:
- Unique, complex passwords for each device.
- Multi-factor authentication (MFA) for added security.
- Secure protocols such as HTTPS and SSH for device management.
Monitoring IoT Devices Behind a Firewall
Utilizing Security Information and Event Management (SIEM)
Security Information and Event Management (SIEM) tools provide real-time monitoring and analysis of network activity. By integrating SIEM with your firewall, you can:
- Monitor IoT device behavior for anomalies.
- Receive alerts for potential security incidents.
- Generate reports for compliance and auditing purposes.
Conducting Regular Security Audits
Regular security audits are essential for identifying vulnerabilities and ensuring compliance with security policies. During audits, assess:
- Firewall configurations and rules.
- IoT device firmware versions and security settings.
- Network segmentation and access controls.
Compliance and Regulatory Considerations
Managing IoT devices behind a firewall is not only about security but also about compliance with industry regulations. Depending on your industry, you may need to adhere to standards such as:
- General Data Protection Regulation (GDPR).
- Health Insurance Portability and Accountability Act (HIPAA).
- Payment Card Industry Data Security Standard (PCI DSS).
Ensure that your firewall and IoT management practices align with these regulations to avoid legal and financial consequences.
Future Trends in IoT Security
Emerging Technologies for IoT Security
The field of IoT security is rapidly evolving, with new technologies emerging to address existing challenges. Some promising trends include:
- Blockchain: Using blockchain for secure device authentication and data integrity.
- Artificial Intelligence: Leveraging AI for predictive threat analysis and automated response.
- Zero Trust Architecture: Implementing a zero-trust model to verify every device and user.
Preparing for the Future
To stay ahead of the curve, it's essential to continuously educate yourself and your team about the latest IoT security trends. Invest in training programs and certifications to enhance your expertise in this area. Additionally, collaborate with industry experts and vendors to explore innovative solutions for securing IoT devices.
Tools and Resources for Managing IoT Behind a Firewall
Recommended Firewall Solutions
Here are some popular firewall solutions that are well-suited for managing IoT devices:
- Palo Alto Networks: Offers advanced threat prevention and IoT-specific features.
- Fortinet: Provides comprehensive network security and segmentation capabilities.
- Cisco ASA: Combines firewall, intrusion prevention, and advanced threat protection.
Free Resources for Learning IoT Security
There are numerous free resources available for learning about IoT security. Some recommended resources include:
- CISA (Cybersecurity and Infrastructure Security Agency)
- NIST (National Institute of Standards and Technology)
- OWASP (Open Web Application Security Project)
Conclusion
In conclusion, managing IoT devices behind a firewall is a critical component of modern cybersecurity. By implementing the strategies and best practices outlined in this article, you can effectively secure your IoT devices, enhance network performance, and protect sensitive data. Remember to regularly update your knowledge and tools to stay ahead of emerging threats.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore our other articles for more insights into cybersecurity and IoT management. Together, we can create a safer digital world.


![Decoding Movie Rules: Understanding & Enjoying Films | [Movierulz] & Beyond](https://silver.isevcloud.co.uk/uploads/3-movierulz-brings-the-latest-hollywood-movierulz-news-3movierulz-also-brings-movie-news-tv-news-trailers-reviews-movierulz-articles-in-south-ind-movies-are-more-than-just-a-form-of-entertainment-they-are-a-reflection-of-culture-storytelling-and-human-emotions-understanding-the-rules-that-govern-films-can-enhance-your-viewing-experience-and-provide-deeper-insights-into-the-narratives-presented-in-this-article-we-will-explore-the-five-essential-movie-rules-that-every-cinephile-should-know-before-movierulz-2025-latest-hd-telugu-kannada-tamil-south-indian-movies-web-series-shows-kdramas-watch-at-high-quality-on-movierulz-tv-this-page-is-intended-to-document-significant-changes-to-the-movie-rules-over-the-course-of-the-site-u2019s-history-this-is-far-from-a-complete-list-with-emphasis-being-placed-on-more-recent-rule-changes-standard-goals-based-on-di-u2026-understanding-movierules-is-essential-for-filmmakers-producers-and-even-audiences-these-regulations-impact-everything-from-the-production-phase-to-distribution-and-viewership-by-adhering-to-these-rules-filmmakers-can-navigate-the-complex-landscape-of-content-creation-ensuring-their-work-is-both-legally-compliant-and-culturally-sensitive-movie-show-times-schedules-and-tickets-in-los-angeles-long-beach-anaheim-santa-ana-irvine-burbank-lakewood-santa-monica-fountain-valley-orange-pasadena-ca-when-it-comes-to-enjoying-films-understanding-the-core-principles-that-govern-cinematic-storytelling-can-elevate-your-viewing-experience-significantly-the-5-movie-rules-com-framework-offers-a-set-of-guidelines-designed-to-help-both-filmmakers-and-audiences-appreciate-the-intricacies-of-modern-cinema-in-this-article-we-will-explore-these-five-essential-rules-and-this-combination-of-comfort-variety-and-free-access-makes-movierulz-profoundly-attractive-especially-for-viewers-on-a-tight-budget-the-dark-side-of-piracy-we-would-like-to-show-you-a-description-here-but-the-site-won-u2019t-allow-us-movierulz-com-movierulz-latest-bollywood-and-hollywood-movies-watch-online-full-free-movierulz-is-wide-range-collection-of-telugu-movies-tamil-malayalam-bengali-kannada-movierulz-movierulz-provide-a-wide-range-of-telugu-movies-tamil-malayalam-and-hindi-movies-watch-full-telugu-movies-online-anytime-anywhere-on-zee5-also-explore-41-telugu-movies-online-in-full-hd-from-our-latest-telugu-movies-collection-movies-are-more-than-just-a-form-of-entertainment-they-are-a-reflection-of-culture-storytelling-and-human-emotions-understanding-the-rules-that-govern-films-can-enhance-your-viewing-experience-and-provide-deeper-insights-into-the-narratives-presented-in-this-article-we-will-explore-the-five-essential-movie-rules-that-every-cinephile-should-know-before-movierulz-latest-featured-telugu-movies-watch-online-download-full-free-collection-of-bollywood-movies-tamil-malayalam-dubbed-kannada-5movierulz-movierulz-is-a-piracy-website-that-leaks-the-tamil-telugu-kannada-hindi-movies-and-allows-users-to-download-movies-in-free-check-out-the-latest-news-and-updates-on-meta-movierulz-here-enjoy-watching-new-telugu-movies-release-of-2025-experience-the-latest-and-new-south-indian-movies-on-your-mobile-device_720.jpg)
