How to Manage IoT Devices Behind a Firewall: A Comprehensive Guide
In today's interconnected world, managing IoT devices behind a firewall is an essential skill for IT professionals and network administrators. As the Internet of Things continues to grow, the need for secure device management becomes increasingly critical. This article will provide you with a detailed understanding of how to effectively manage IoT devices while maintaining robust security measures.
IoT devices are revolutionizing industries by enabling smarter, more efficient operations. However, these devices also introduce new security challenges. Ensuring that IoT devices function securely within a network requires a strategic approach to firewall management and device configuration.
This guide will cover everything you need to know about managing IoT devices behind a firewall, including best practices, real-world examples, and actionable tips. Whether you're a beginner or an experienced IT professional, this article will provide valuable insights to enhance your knowledge.
Understanding IoT Devices and Firewalls
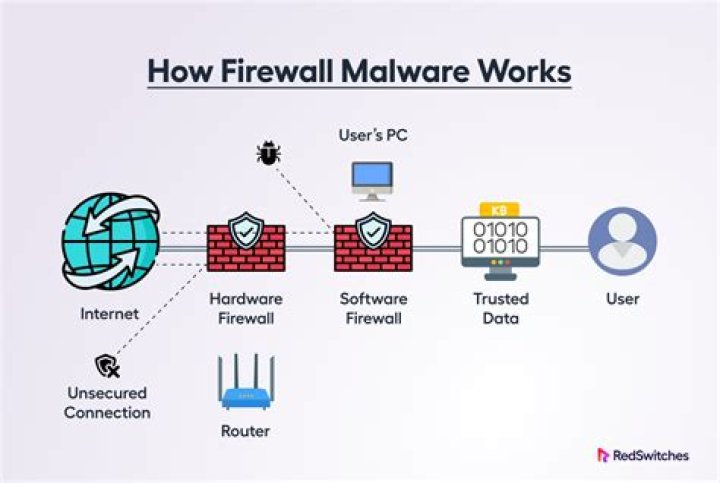
IoT devices are physical objects embedded with sensors, software, and connectivity that enable them to exchange data with other devices and systems over the internet. Firewalls, on the other hand, act as a barrier between trusted and untrusted networks, controlling incoming and outgoing traffic based on predetermined security rules.
When IoT devices are deployed within a network, they must be properly configured to work behind a firewall. This involves setting up firewall rules, ensuring proper authentication, and implementing encryption protocols to protect sensitive data.
According to a report by Gartner, the number of connected IoT devices is expected to exceed 25 billion by 2025, highlighting the growing importance of secure device management.
Why Managing IoT Devices Behind a Firewall Matters
Managing IoT devices behind a firewall is crucial for maintaining network security and preventing unauthorized access. Without proper configuration, IoT devices can become vulnerable to cyberattacks, data breaches, and other security threats.
Some key reasons why managing IoT devices behind a firewall is important include:
- Preventing unauthorized access to your network.
- Protecting sensitive data transmitted by IoT devices.
- Ensuring compliance with industry regulations and standards.
- Improving overall network performance and reliability.
By implementing robust firewall policies and device management strategies, organizations can significantly reduce the risk of security incidents and protect their valuable assets.
Key Challenges in Managing IoT Devices Behind a Firewall
Device Compatibility Issues
One of the main challenges in managing IoT devices behind a firewall is ensuring compatibility between different devices and network protocols. Many IoT devices use proprietary communication protocols, which can complicate the process of integrating them into a secure network environment.
To address this issue, network administrators should carefully evaluate the compatibility of IoT devices before deployment and implement standardized communication protocols whenever possible.
Network Bandwidth Constraints
Another challenge is managing network bandwidth effectively. IoT devices often generate large amounts of data, which can strain network resources and impact performance. To mitigate this issue, organizations should implement quality of service (QoS) policies and prioritize critical traffic to ensure smooth operation.
Security Vulnerabilities
IoT devices are frequently targeted by cybercriminals due to their potential vulnerabilities. Weak authentication mechanisms, outdated firmware, and insufficient encryption can all contribute to security risks. Network administrators must stay vigilant and implement strong security measures to protect IoT devices and the networks they operate on.
Best Practices for Managing IoT Devices Behind a Firewall
Successfully managing IoT devices behind a firewall requires a combination of technical expertise, strategic planning, and ongoing monitoring. Below are some best practices to help you achieve effective device management:
- Implement strong authentication and authorization protocols.
- Regularly update device firmware and software to address security vulnerabilities.
- Segment IoT devices into separate network zones to isolate potential threats.
- Monitor device activity and network traffic for suspicious behavior.
- Use encryption to protect sensitive data transmitted by IoT devices.
By following these best practices, organizations can create a secure and efficient environment for managing IoT devices behind a firewall.
Real-World Example: Managing IoT Devices in a Corporate Network
To illustrate the process of managing IoT devices behind a firewall, consider the following real-world example:
A large manufacturing company recently deployed a network of IoT sensors to monitor equipment performance and optimize production processes. To ensure secure device management, the company implemented the following strategies:
- Configured firewall rules to allow only necessary traffic to and from IoT devices.
- Segmented IoT devices into a dedicated VLAN to isolate them from the main corporate network.
- Implemented multi-factor authentication for all IoT device access.
- Enabled encryption for all data transmitted by IoT devices.
As a result of these measures, the company successfully reduced the risk of security breaches and improved overall network performance.
Setting Up Firewall Rules for IoT Devices
Identifying Necessary Ports and Protocols
When configuring firewall rules for IoT devices, it's essential to identify the ports and protocols required for proper device operation. This involves reviewing the device documentation and understanding the communication requirements of each device.
Some common ports and protocols used by IoT devices include:
- HTTP/HTTPS (ports 80/443) for web-based communication.
- MQTT (port 1883) for lightweight messaging between devices.
- CoAP (port 5683) for constrained device communication.
By allowing only the necessary ports and protocols, organizations can minimize the attack surface and enhance network security.
Implementing Access Control Lists (ACLs)
Access control lists (ACLs) are a powerful tool for managing IoT devices behind a firewall. ACLs allow network administrators to define specific rules for controlling traffic to and from IoT devices, ensuring that only authorized devices and users can access the network.
To implement ACLs effectively, organizations should:
- Define clear access policies based on device type and function.
- Regularly review and update ACLs to reflect changes in the network environment.
- Monitor access logs for suspicious activity and adjust rules as needed.
By using ACLs, organizations can create a secure and controlled environment for managing IoT devices.
Monitoring and Maintaining IoT Device Security
Ongoing monitoring and maintenance are critical components of effective IoT device management. Network administrators should regularly review device configurations, update firmware, and analyze network traffic to identify potential security threats.
Some key strategies for monitoring and maintaining IoT device security include:
- Implementing intrusion detection and prevention systems (IDPS) to detect and respond to suspicious activity.
- Conducting regular security audits to identify vulnerabilities and address them proactively.
- Training employees on best practices for IoT device management and security.
By staying vigilant and addressing security issues promptly, organizations can ensure the long-term safety and reliability of their IoT deployments.
Tools and Technologies for Managing IoT Devices Behind a Firewall
Several tools and technologies are available to help organizations manage IoT devices behind a firewall more effectively. These include:
- Network management platforms that provide centralized control over IoT devices and network resources.
- Firewall solutions designed specifically for IoT environments, offering advanced features such as deep packet inspection and application-aware filtering.
- Security information and event management (SIEM) systems for monitoring and analyzing IoT device activity.
By leveraging these tools and technologies, organizations can streamline the process of managing IoT devices and enhance overall network security.
Future Trends in IoT Device Management
As the IoT landscape continues to evolve, new trends and technologies are emerging that will shape the future of device management. Some of these trends include:
- Increased adoption of edge computing to reduce latency and improve device performance.
- Development of AI-driven security solutions for detecting and responding to threats in real-time.
- Standardization of communication protocols to improve device interoperability and simplify management.
Staying informed about these trends and incorporating them into your IoT strategy can help you stay ahead of the curve and maximize the benefits of your IoT deployment.
Conclusion
Managing IoT devices behind a firewall is a critical task for ensuring network security and protecting sensitive data. By understanding the challenges involved, implementing best practices, and leveraging the right tools and technologies, organizations can create a secure and efficient environment for their IoT deployments.
We encourage you to take action by reviewing your current IoT device management practices and identifying areas for improvement. Share your thoughts and experiences in the comments below, and don't forget to explore other articles on our site for more insights into IoT and network security.



