Redd.it Malware: Understanding the Threat and Protecting Your System
Redd.it malware has become a growing concern for internet users worldwide. This malicious software poses significant risks to your digital security and privacy. In this comprehensive guide, we will delve into the nature of this threat, its impact, and how you can safeguard your devices. If you're worried about redd.it malware, you're in the right place.
As cyber threats evolve, understanding redd.it malware is crucial for maintaining the integrity of your digital environment. This article aims to provide you with actionable insights and practical advice to help protect your system from potential harm.
Whether you're a tech-savvy individual or a casual user, this guide will equip you with the knowledge to identify redd.it malware and take necessary precautions. Let's explore this topic in detail and learn how to stay safe online.
What is Redd.it Malware?
Redd.it malware refers to a specific type of malicious software that targets users through the popular social media platform Reddit. This malware often disguises itself as legitimate content, such as links or downloads, making it challenging for users to identify. Once installed, it can compromise personal data, steal sensitive information, or disrupt system performance.
The primary goal of redd.it malware is to exploit vulnerabilities in users' systems, often leading to unauthorized access or financial losses. Understanding its origins and mechanisms is essential for effective prevention.
History of Redd.it Malware
Redd.it malware first emerged as a concern when users reported suspicious activity linked to Reddit. Over time, it has evolved into a sophisticated threat, leveraging advanced techniques to bypass security measures.
Common Types of Redd.it Malware
There are several types of redd.it malware, each with unique characteristics and methods of operation. Below, we outline the most prevalent forms:
- Adware: Displays intrusive ads and collects browsing data.
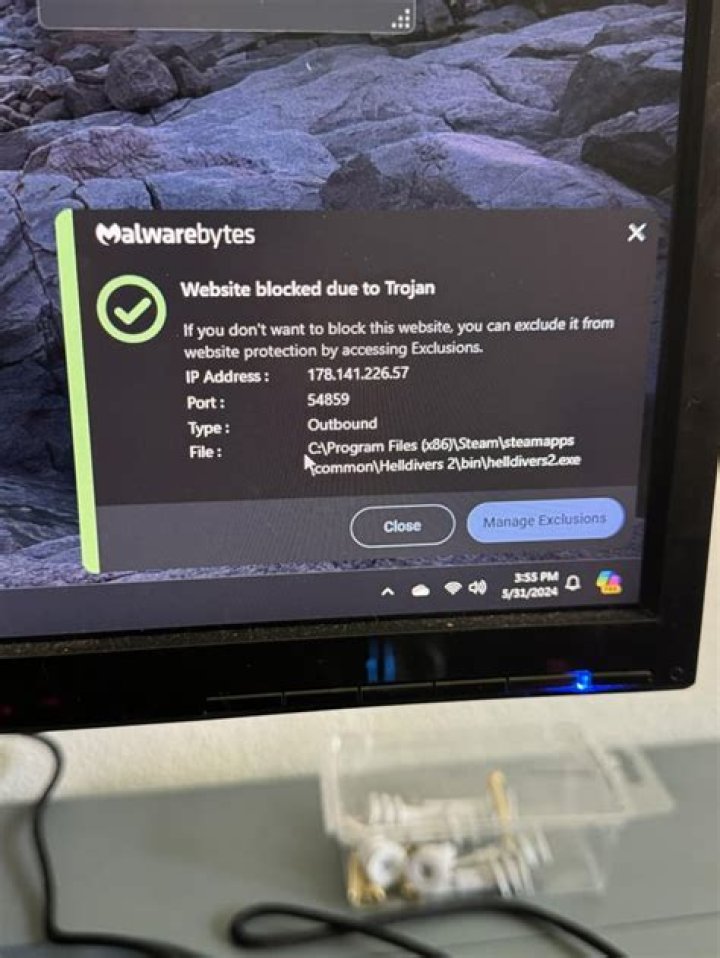
- Trojans: Disguises itself as legitimate software to infiltrate systems.
- Ransomware: Encrypts files and demands payment for decryption.
- Keyloggers: Records keystrokes to steal passwords and sensitive information.
Understanding the Differences
Each type of redd.it malware poses distinct risks. For instance, adware primarily affects user experience, while ransomware can lead to severe financial consequences. Recognizing these differences is key to addressing the appropriate countermeasures.
How Redd.it Malware Spreads
Redd.it malware spreads through various channels, including:
- Malicious links shared in comments or posts.
- Phishing emails pretending to be from Reddit.
- Compromised accounts used to distribute infected content.
User behavior plays a significant role in the propagation of redd.it malware. Clicking on unfamiliar links or downloading unverified files increases the likelihood of infection.
Role of Social Engineering
Social engineering tactics are often employed to deceive users into downloading redd.it malware. These tactics exploit human psychology, making it crucial to remain vigilant and skeptical of suspicious content.
Signs Your System is Infected
Identifying redd.it malware early is vital for minimizing damage. Common signs include:
- Unusual pop-ups or advertisements.
- Sluggish system performance.
- Unexplained data usage or network activity.
- Unexpected changes to browser settings.
Regularly monitoring your system for these symptoms can help detect and address infections promptly.
Advanced Detection Techniques
Utilizing antivirus software and regular system scans can enhance detection capabilities. Additionally, enabling real-time protection features provides an extra layer of security against redd.it malware.
Prevention Strategies Against Redd.it Malware
Preventing redd.it malware involves adopting proactive measures. Below are some effective strategies:
- Install reputable antivirus and anti-malware software.
- Keep your operating system and applications up to date.
- Avoid clicking on suspicious links or downloading unknown files.
- Use strong, unique passwords for all accounts.
By implementing these practices, you significantly reduce the risk of redd.it malware compromising your system.
Education and Awareness
Staying informed about the latest cyber threats and prevention techniques is crucial. Regularly educating yourself and others about redd.it malware helps foster a safer digital environment.
The Removal Process
If your system is infected with redd.it malware, immediate action is necessary. Follow these steps for effective removal:
- Disconnect from the internet to prevent further data transmission.
- Boot your computer in safe mode to limit malware activity.
- Run a full system scan using trusted antivirus software.
- Remove any identified threats and reset affected settings.
Seeking professional assistance for complex cases ensures thorough removal and restoration of your system.
Post-Removal Steps
After removing redd.it malware, take additional steps to secure your system. Update all software, change passwords, and monitor for any lingering issues.
Impact of Redd.it Malware on Users
The effects of redd.it malware can be devastating, impacting both individuals and organizations. Potential consequences include:
- Data breaches leading to identity theft.
- Financial losses due to unauthorized transactions.
- Reputational damage from compromised accounts.
Understanding these impacts underscores the importance of proactive cybersecurity measures.
Legal and Ethical Considerations
Redd.it malware not only affects users but also raises legal and ethical concerns. Developers and distributors of such malware may face severe legal repercussions, emphasizing the need for responsible digital behavior.
Case Studies: Real-Life Examples
Examining real-world instances of redd.it malware provides valuable insights into its operation and impact. Below are two notable cases:
Case Study 1: Large-Scale Data Breach
In 2021, a redd.it malware campaign resulted in a significant data breach affecting thousands of users. The attackers exploited vulnerabilities in outdated software, highlighting the importance of regular updates.
Case Study 2: Targeted Phishing Attack
A targeted phishing attack using redd.it malware compromised several corporate accounts. This incident underscored the need for employee training and robust security protocols.
Expert Advice for Enhanced Security
Cybersecurity experts recommend the following practices to enhance protection against redd.it malware:
- Implement multi-factor authentication for all accounts.
- Regularly back up important data to prevent loss.
- Stay informed about emerging threats and prevention strategies.
By following expert advice, you fortify your defenses and minimize the risk of redd.it malware infiltration.
Building a Secure Digital Environment
Creating a secure digital environment involves a combination of technology, education, and vigilance. Adopting a proactive approach ensures long-term protection against redd.it malware and other cyber threats.
Conclusion
Redd.it malware poses a significant threat to digital security, but with the right knowledge and tools, you can protect your system effectively. By understanding its nature, recognizing signs of infection, and implementing prevention strategies, you significantly reduce the risk of falling victim to this malicious software.
We encourage you to share this article with others and explore additional resources on our website. Together, we can foster a safer online community. Stay informed, stay vigilant, and stay secure!



